Product Update - v22.12
Features
Automated component deployments
In platform version 22.12 we are releasing the new automated component deployment feature. We introduced the underlying concept with the version 22.04 release at the end of January 2022. Here is the final workflow of the automated component deployments:
- A new version (
tag) is created in the GitHub component repository and the release is published. - The CircleCI build process uses
appbuilder+apprunnerimages. - A Docker image of the component is built with the
tagversion and submitted to Dockerhub. - An additional
latestversion is created in Dockerhub each time the code is updated. - The platform runs a Kubernetes platform job called
components-pusherat certain intervals checking the component Dockerhublatestversion. - If the version in Dockerhub differs from the existing platform version it pulls a new Docker image and pushes it into the platform docker registry.
- A new version of component is released for the platform users and can be selected while designing flows.
Please Note - we determine and set the configuration of platform
components-pusherin HELM3 deployment charts. These configurations provide more options for each component. Here we present the typical scenario.
The automated component deployment process works along with the old git-push
workflow. You can push components via git receiver as well. The components-pusher will not
interfere with your pushed version.
Improvements and Updates
Node.js Sailor version 2.6.27
We released a new version (2.6.27) of the Node.js Sailor library version. This
version includes an npm audit to CI and updated dependencies.
UX Improvements: credentials page
To improve the user experience on the credentials page we added the component team and repository name to which this credential belongs. This helps in distinguishing between different deployments of components and in choosing the correct component for credential modification.
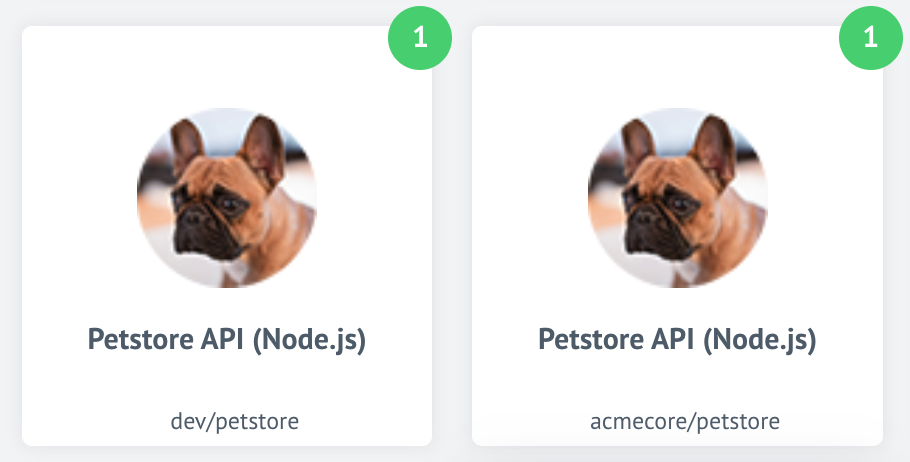
The above images show two different repositories of the same component. The new improvement shows the difference between these two components.
HELM3
We constantly improve different aspects of HELM3 deployments in collaboration with our partners. This section lists updates and improvements done in this round.
Configure password length and rules
With platform version 22.12 we introduce a new configuration to set the login password length and the requirements. The following variables have been added to HELM3 charts:
MIN_PASSWORD_LENGTH- the user password must have at least this number of symbols,MIN_PASSWORD_RULES_MATCHES- number of minimum different character groups (uppercase, lowercase, numbers, special symbols) should be matched
Session timeout configuration
To provide more granular control for session timeout and distinguish between idle
and absolute timeouts we introduce new configurations and deprecate the COOKIE_MAX_AGE
environment variable. The idle and absolute timeouts follow definitions described
in the OWASP. We also introduce the HELM3 configuration variables to control values
for these new timeouts:
SESSION_IDLE_TIMEOUT- default: 24 hours - replacesCOOKIE_MAX_AGE,SESSION_ABSOLUTE_TIMEOUT- default:2times theSESSION_IDLE_TIMEOUT.
Fixed bugs
- Addressed the issue when the “Server error” message would show while navigating through the UI upon the session expiration.
- Fixed the bug causing the system to erroneously send “New sign-in to your account” emails. The expired sessions were not deleted from the system.
- Addressed the issue with the “Mapping” configuration field showing up in UI for the trigger functions on components.
Components
With introduction of automated component pusher we change the standardise component
build procedures preparing them for components-pusher service. The following component
build configurations were changed:
- GraphQL component
1.1.1 - CSV component v3
3.1.1 - JDBC component
2.5.1 - SOAP component
1.2.8 - Shopify Admin Component
1.5.0
GraphQL component 1.1.1
- ADDED
No Auth,Basic AuthandAPI Key Authauthentication methods - ADDED a new action
Raw Request - ADDED a new action
Configured Request
Shopify admin component 1.5.0
- ADDED: a new action
Update Inventory Level - FIXED the output metadata for
Get New And Updated Objects Pollingtrigger
PayPal component 1.0.0
- ADDED: a new action
Make Raw Request
Vtex component 1.2.0
- ADDED: a new action
Lookup Set Of Objects By Unique Criteria